Gen AI-Powered Threat Investigation & Explainable SOC Automation
CyberTiX AI
DETECT, DEFEND AND DECIDE.
AT AI SPEED.
CyberTiX AI is an AI-native cybersecurity platform that augments your existing SIEM, EDR, Cloud, and Network stack with explainable AI, Large Security Model (LSM) intelligence, and agentic automation, transforming how modern SOC teams investigate and respond to threats.
30–60%
Alert Noise Reduction
40–70%
Faster Incident Response
Audit-Ready
Evidence-Bound Decisions
up to 70%
MTTR Reduction
THE ENTERPRISE PROBLEM
Security Teams Are Drowning. Attackers Are Winning.
- 3,000–8,000 alerts per day, most go unreviewed
- AI-powered attacks exploiting automation gaps
- 6–9 month attacker dwell times
- Fragmented context across SIEM, EDR, Cloud, Identity, SaaS
- Black-box AI tools that erode trust
- Growing regulatory scrutiny (RBI, SEBI, OCC, EU AI Act, NIST AI RMF)
- They don’t explain.
- They don’t correlate intelligently.
- They don’t provide board-ready evidence.
Modern enterprises need more than detection.
They need explainable, evidence-backed AI-driven security operations.
WHAT IS CYBERTIX AI?
AI for Security. Built for Modern SOCs.
- Overlay (not replace) your current security stack
- Collapse alerts into structured, explainable cases
- Deliver evidence-bound AI narratives
- Automate incident response with policy-aware controls
- Provide regulator-ready audit trails
- Generative AI
- Agentic AI automation
- Threat intelligence enrichment
- MITRE ATTACK mapping
- Business-context awareness
- Deterministic policy gates
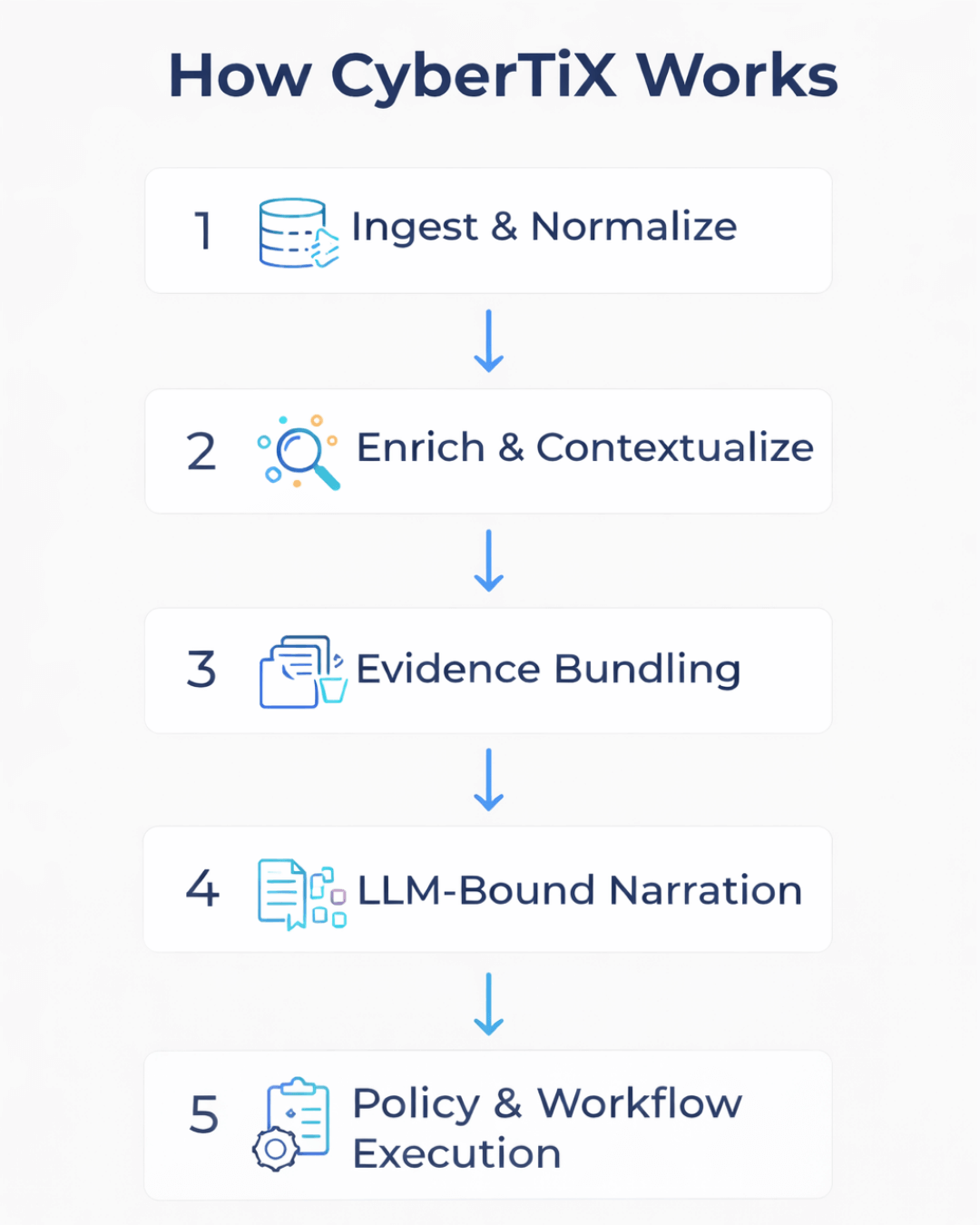
How CyberTiX Works
From Raw Alerts to Explainable Decisions
Ingest & Normalize
Map and unify security telemetry across network, EDR, identity, cloud, and PCAP/NetFlow sources to ensure complete visibility while preserving original source provenance.Enrich & Contextualize
Correlate alerts with asset registry data, user context, threat intelligence feeds, and behavioral baselines to align detections with operational reality.Evidence Bundling
Create compact, structured case bundles that include log snippets, detection logic, risk scores, timeline reconstruction, and MITRE ATT&CK mappings for defensible analysis.LLM-Bound Narration
Use a bounded, evidence-constrained LLM to generate a clear threat narrative, confidence score, counterfactual analysis (what would increase or decrease confidence), and recommended next steps with no hallucinations or speculative output.Policy & Workflow Execution
Apply deterministic decision gates to suppress, escalate, contain, or trigger SOAR/ITSM workflows, with human-in-the-loop oversight for critical actions.
CORE CAPABILITIES
Enterprise-Grade AI-Powered Security Operations
Autonomous signal correlation across PCAP, NetFlow, DNS, HTTP/S, SSH, endpoints.
Natural language security queries with explainable outputs.
LSM-powered playbooks trigger real-time containment and remediation.
Risk-based prioritization using real-time exploitability + business criticality.
LLM-enhanced behavioral analytics with business owner routing.
Simulates network behavior to predict potential breach impact.
Cost-efficient intelligence sharing and adaptive learning.
Every action includes source-linked evidence, Rationale, Confidence level, and Traceable lineage.
SECURITY CENTER & FULL-STACK VISIBILITY
- DNS, SSH, HTTP, HTTPS deep inspection
- Protocol anomaly detection
- IDS log correlation
- Threat feed integration
- PCAP forensic access
- Device monitoring
- Process intelligence
- Package vulnerability tracking
- User activity analytics
- Behavioral anomaly detection
- Transaction flow visibility
- Performance bottleneck detection
- Component-level security mapping
- Application health intelligence
- Asset exposure tracking
- Network interface health
- Configuration drift detection
It’s AI-powered security intelligence across your digital ecosystem
BUSINESS OUTCOMES
Measurable ROI in 3–6 Months
30–60% Reduction
Alert Noise
↓ 40–70%
MTTR
↓ 40%
Analyst Workload
3–10× faster
Investigation Speed
↑ 50%
Detection Accuracy
↓ 30–40%
Audit Prep Time
Less burnout
Fewer false positives
Faster containment
Lower breach cost
VALUE BY STAKEHOLDER
Board-ready evidence, measurable risk reduction, explainable AI.
Fewer tickets. Faster triage. Reduced context switching.
Policy-to-action traceability with exportable evidence packs.
Reduced breach cost and operational efficiency gains.
Higher margins, faster onboarding, multi-tenant scalability.
WHY CYBERTIX IS DIFFERENT
Not Another AI Tool. A Security Intelligence Brain.
Proprietary Semantic Large Security Model
Evidence-Bound AI (No hallucinations)
Audit-Ready by Architecture
Business & Policy-First Design
Integration-First Deployment (< 1 month value realization)
Future-Ready for Agentic Co-Pilot Evolution
CyberTiX is designed for tomorrow’s AI-driven enterprise risk landscape.
ENGAGEMENT MODELS
Flexible. Modular. Enterprise-ready.

Managed AI for Security (24×7 Delivery)
Co-Managed SOC
MSSP Integrated Model
Advisory Retainer Model
Future-Proof Your AI with CyberTiX AI
Start Securing Your Business Today!
We’re a full-stack platform for AI for security and security for AI.
- marketing@cygeniq.com
Platform
Solutions
Company
Policies
Be the First to Know
Stay Ahead in Cybersecurity – Subscribe to Our Newsletter for Insights, Updates, and Expert Tips!
© 2026 Cygeniq AI. All Rights Reserved.
- 1207 Delaware Ave, Suite # 3041 Wilmington , DE 19806, USA